
Shannon Anderson
-
 Read more: 10 Essential MSP Cloud Security Measures for Secure Data Protection
Read more: 10 Essential MSP Cloud Security Measures for Secure Data ProtectionIn today’s digital age, the need for robust cloud security measures is more critical than ever. From protecting sensitive data to ensuring business continuity, Managed Service Providers (MSPs) play a crucial role in safeguarding their clients’ information. By implementing network security, data encryption, access control, disaster recovery planning, and regular […]
-
 Read more: Maximizing Efficiency with RMM Device Monitoring Best Practices
Read more: Maximizing Efficiency with RMM Device Monitoring Best PracticesIn the world of IT management, RMM (Remote Monitoring and Management) device monitoring plays a crucial role in maintaining the health and security of an organization’s network. From setting up automated alerts to conducting regular security audits, there are a number of best practices that can ensure your RMM device […]
-
 Read more: Maximizing Efficiency: A Guide to Homebrew Software Dependency Tracking
Read more: Maximizing Efficiency: A Guide to Homebrew Software Dependency TrackingHave you ever wondered how homebrew software manages its dependencies? In this article, we will explore the importance of dependency tracking in homebrew software, how it works, and the benefits and challenges it presents. We will also discuss different methods for implementing dependency tracking and highlight some popular tools used […]
-
 Read more: Optimizing System Health with ConnectWise Automate Procedures
Read more: Optimizing System Health with ConnectWise Automate ProceduresAre you struggling to keep your systems running smoothly and efficiently? We will explore the importance of ConnectWise Automate System Health Checks and why they are crucial for the performance of your systems. We will discuss how often these checks should be performed and outline the step-by-step procedures for conducting […]
-
 Read more: Optimize Your System with BleachBit’s Best Practices for Temporary File Cleanup
Read more: Optimize Your System with BleachBit’s Best Practices for Temporary File CleanupAre you looking to improve your computer’s performance, enhance security, and free up storage space? BleachBit may be the solution for you. In this article, we will explore what BleachBit is, the importance of cleaning up temporary files, best practices for using the software, the benefits it offers, potential risks […]
-
 Read more: Boost Your Linux System: Apt-Get Package Backup Strategies
Read more: Boost Your Linux System: Apt-Get Package Backup StrategiesAre you familiar with Apt-Get and the importance of backing up its packages? This article explores different backup strategies for Apt-Get packages, including manual, automated, and snapshot backups. We discuss how to perform a manual backup, set up an automated backup using cron jobs or third-party tools, and delve into […]
-
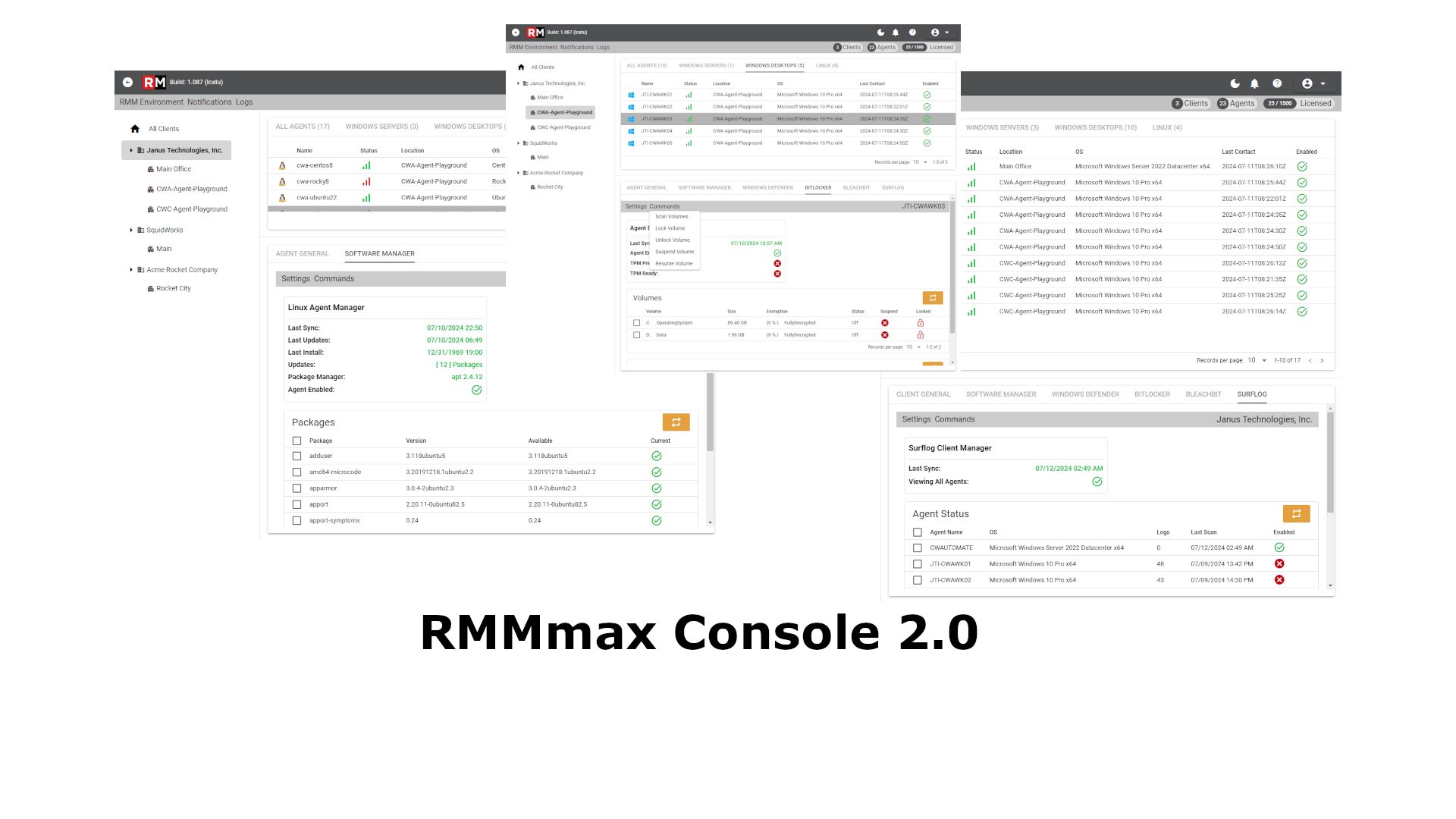 Read more: RMMmax Console 2.0 Development Preview: A Glimpse Behind the Curtain
Read more: RMMmax Console 2.0 Development Preview: A Glimpse Behind the CurtainThe Buzz Is Real You know that feeling when you’re about to unwrap a shiny new gadget? Well, multiply that by ten, add a dash of intrigue, and you’ve got the RMMmax Console 2.0 Development Preview. It’s like the software equivalent of a secret garden—lush, mysterious, and ripe with possibilities. […]
-
 Read more: Boost Your Security: Yum Package Vulnerability Assessment Techniques
Read more: Boost Your Security: Yum Package Vulnerability Assessment TechniquesYum package manager is a crucial tool for managing software packages on Linux systems. Assessing Yum package vulnerabilities is essential to ensure the security of your system. We will explore the different techniques used for Yum package vulnerability assessment, including manual assessment, automated scanning tools like OpenSCAP, Lynis, and Nessus, […]
-
 Read more: Maximizing Efficiency: Chocolatey Package Deployment Strategies
Read more: Maximizing Efficiency: Chocolatey Package Deployment StrategiesChocolatey is a popular package manager for Windows that simplifies the process of installing, updating, and managing software packages. We explore different deployment strategies for Chocolatey packages, including manual deployment, group policy deployment, PowerShell deployment, Puppet deployment, Chef deployment, and Ansible deployment. Learn how to choose the right deployment strategy […]
-
 Read more: Unlocking the Power of RMM with Effective Optimization Strategies
Read more: Unlocking the Power of RMM with Effective Optimization StrategiesAre you looking to enhance the efficiency and effectiveness of your Remote Monitoring and Management (RMM) processes? In this article, we will explore the concept of RMM optimization and why it is essential for businesses. We will discuss the benefits of implementing RMM optimization strategies, as well as different approaches […]
Recent Posts
- Optimize Your System with BleachBit: Best Practices for Scheduled Cleanup
- Optimize Your Patching Strategies with Tactical RMM
- Streamline Your Software Update Process with These Homebrew Tips
- Ultimate Guide to BleachBit Temporary File Cleanup: Maximize Your Computer’s Performance
- Ultimate Guide to ConnectWise Automate Configuration Management
Categories
- News 539
Tag Cloud
Apt BitLocker BitLocker Management with Screen Connect BleachBit Chocolatey ConnectWise Automate ConnectWise Control DattoRMM Family Gratitiude Happy Thanksgiving Homebrew How to safe guard BitLocker Recovery Keys across your RMM environment Linux Manage BitLocker with ConnectWise Automate network security practices for businesses Package Managers RMMmax RMMMax Tool RMM or RAT environment RMM Plugins ScreenConnect Software package manager Tactical RMM Thankful Thanksgiving Using Datto RMM to manage BitLocker Windows Defender Yum





